Defending Your Organisation in the Age of Phishing with Training Courses and Technology
Phishing attacks are the cause of over 90% of data breaches in Australia. This article explains how businesses can combat phishing with the combination of information security awareness and anti-phishing technologies.

Phishing attacks are the cause of over 90% of data breaches in Australia. This article explains the consequences of falling victim to phishing and provides a framework for addressing this cyber risk in your business.
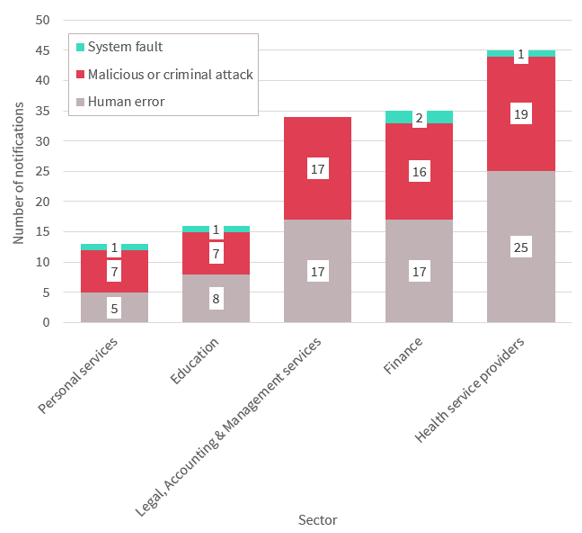
The ACCC Scamwatch reports that Australians lost $340 million during 2017, a $40 million increase over 2016. A portion of these attacks will have been from attackers posing as reputable businesses, impacting on industry reputation. Reputational damage can include your firm becoming a case study in what not to do. No organisation wants that kind of attention.
The public response to the hack of the law firm behind the Panama Papers; Mossack Fonseca demonstrates that businesses cannot expect public opinion to be on their side. Quite to the contrary, the increasing number of data breaches abroad and locally impact on public trust in organisations and institutions more broadly. Customers can hardly be blamed for their anger given that their sensitive data can be published online or exploited for malice and profit.
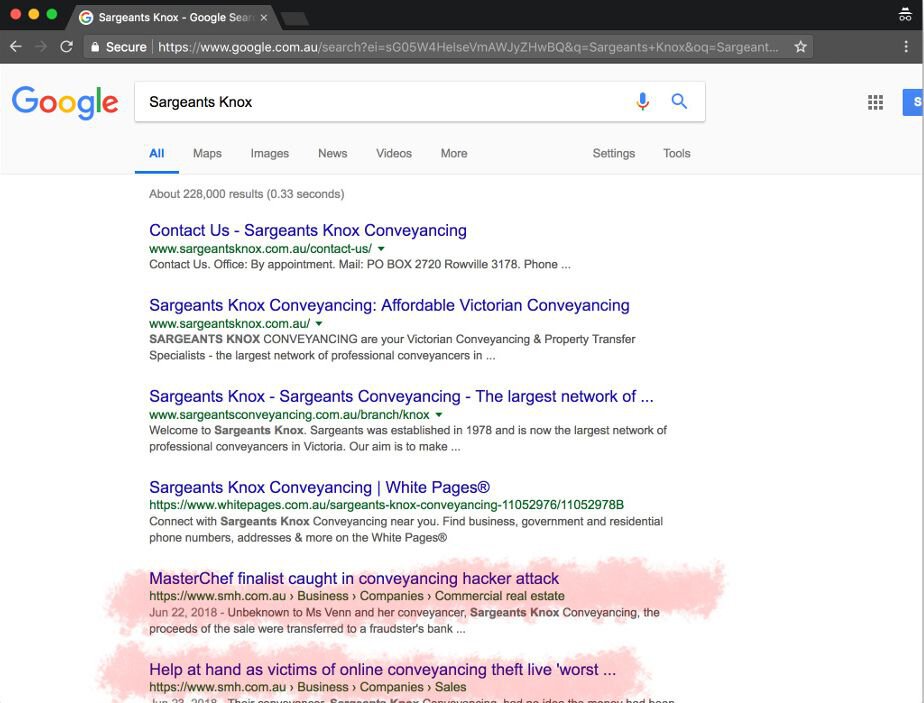
In a report released this week by the OAIC, the office which administers the Notifiable Data Breaches Scheme the industries reporting the highest number of privacy breaches over the last three months have been health service providers, financial services and legal, accounting and management services.
"Everyone who handles personal information in their work needs to understand how data breaches can occur so we can work together to prevent them," – [the Privacy Commissioner] Ms Falk said.
Should organisations and their customers consider a data breach an inevitable consequence of doing business? The imminent threat does not mean inevitable failure according to Iron Bastion cybersecurity experts who advocate security awareness training to harden organisations against attack.
The more layers of security an organisation has, the less likely it is that it will be successfully hacked as attackers go after low hanging fruit. With computer security training for employees raising email awareness, there is no reason your organisation has to be an easy target.
Iron Bastion see two distinct elements in the prevention of phishing attacks: technology and people.
Technology
Anti-phishing services
As 90% of data breaches happen through phishing, it is important to vet every incoming email for malicious intent. Businesses should subscribe to an email security solution that can identify and block phishing emails.
Refer to our previous article about spam vs. phishing that explains why your spam filter is not enough to defend your business.
Protect your web traffic with a DNS firewall or a proxy server
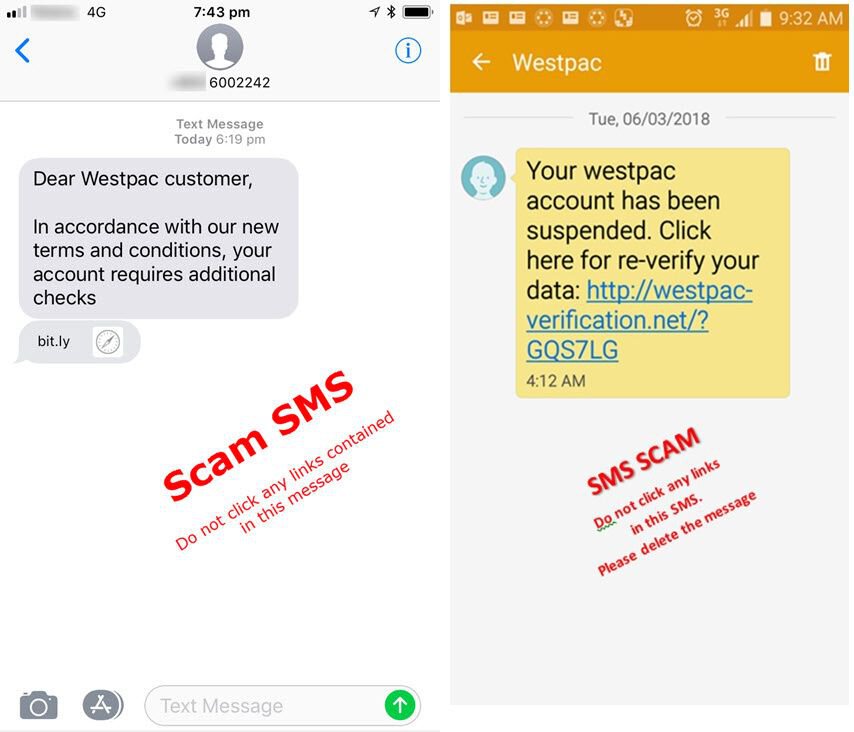
Cybercriminals may try to circumvent the anti-phishing services protecting your work emails. Phishing threats may also arrive via private emails, instant messages or SMS.
Circumvention can also happen if the anti-phishing service is misconfigured. Earlier research we published showed that one in every three Australian law firms are susceptible to a cyber threat called “direct email spool attack”, rendering email security solutions completely useless and exposing the affected organisations to cybercrime.
We suggest businesses augmenting their email security solutions with threat-blocking DNS firewalls and/or proxy services for an additional layer of protection.
Examples of DNS firewalls are:
- Paid: Cisco Umbrella, Cyren, Webroot DNS Protection
- Free: OpenDNS, Quad 9, Norton ConnectSafe
- BYO: Pi-hole
Proxy services include, but not limited to Symantec Secure Web Gateway & Proxy Appliance, Forcepoint Websense and Trend Micro InterScan Web Security.
Endpoint security and antivirus products with built-in protection from phishing
Not every antivirus product is made equal. Better security products can protect your business from phishing. These endpoint security tools can monitor the web browser and block any suspicious activity.
We suggest using one of the products rated as Tier-1 by this independent antivirus assessment (page 12): https://www.mrg-effitas.com/wp-content/uploads/2018/08/MRG-Effitas-2018Q2-360-Assessment.pdf
Two-factor authentication on your email accounts
The most effective protection from Business email compromise fraud. Enforcing Two-factor Authentication (2FA) on your email service is a robust security measure that can protect your business from payment redirection scams and Business Email Compromise (BEC) Fraud.
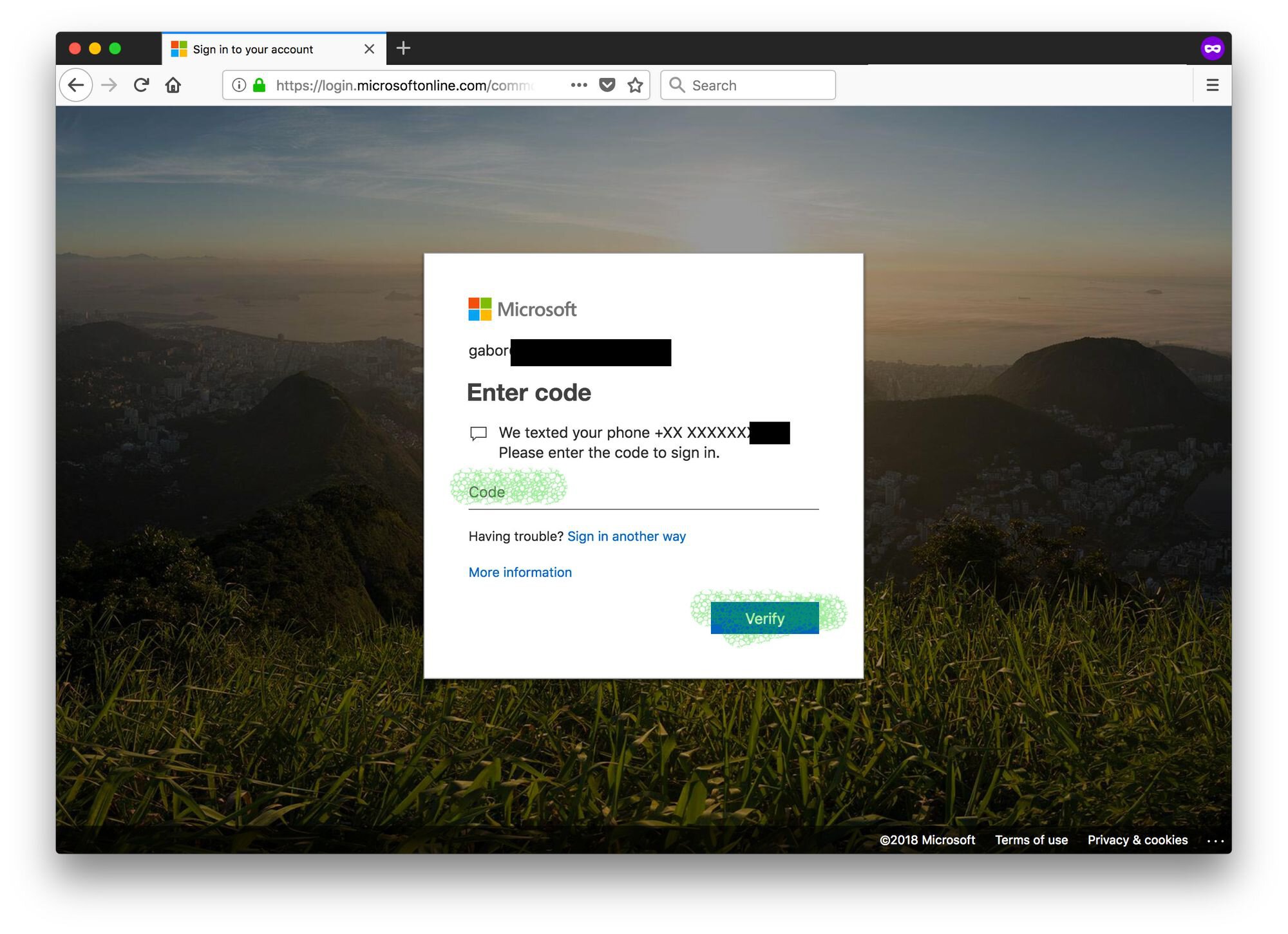
Our article from earlier explains how you can turn on this essential security measure on Office 365 and G Suite.
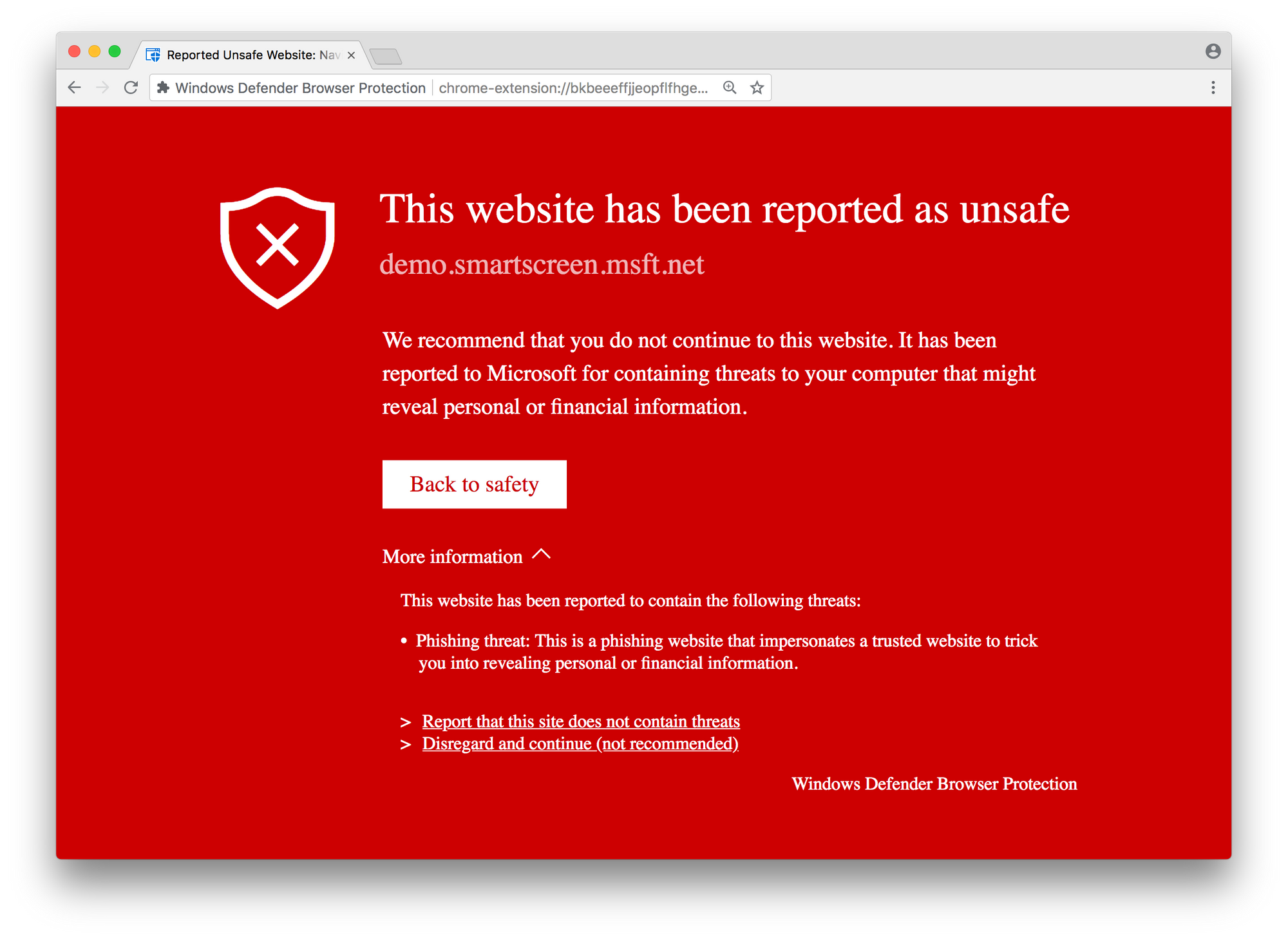
Web browser extensions
Browser extensions can be used to block malicious websites from loading inside the browser.
Examples include Windows Defender, Netcraft Extension and Blockade. If a member of your staff enters their Google password in another (potentially malicious) site, Google’s Password Alert extension will issue a warning and reinforce password best practice. If your organisation uses Firefox, the Netcraft Anti-Phishing Extension is useful.
People
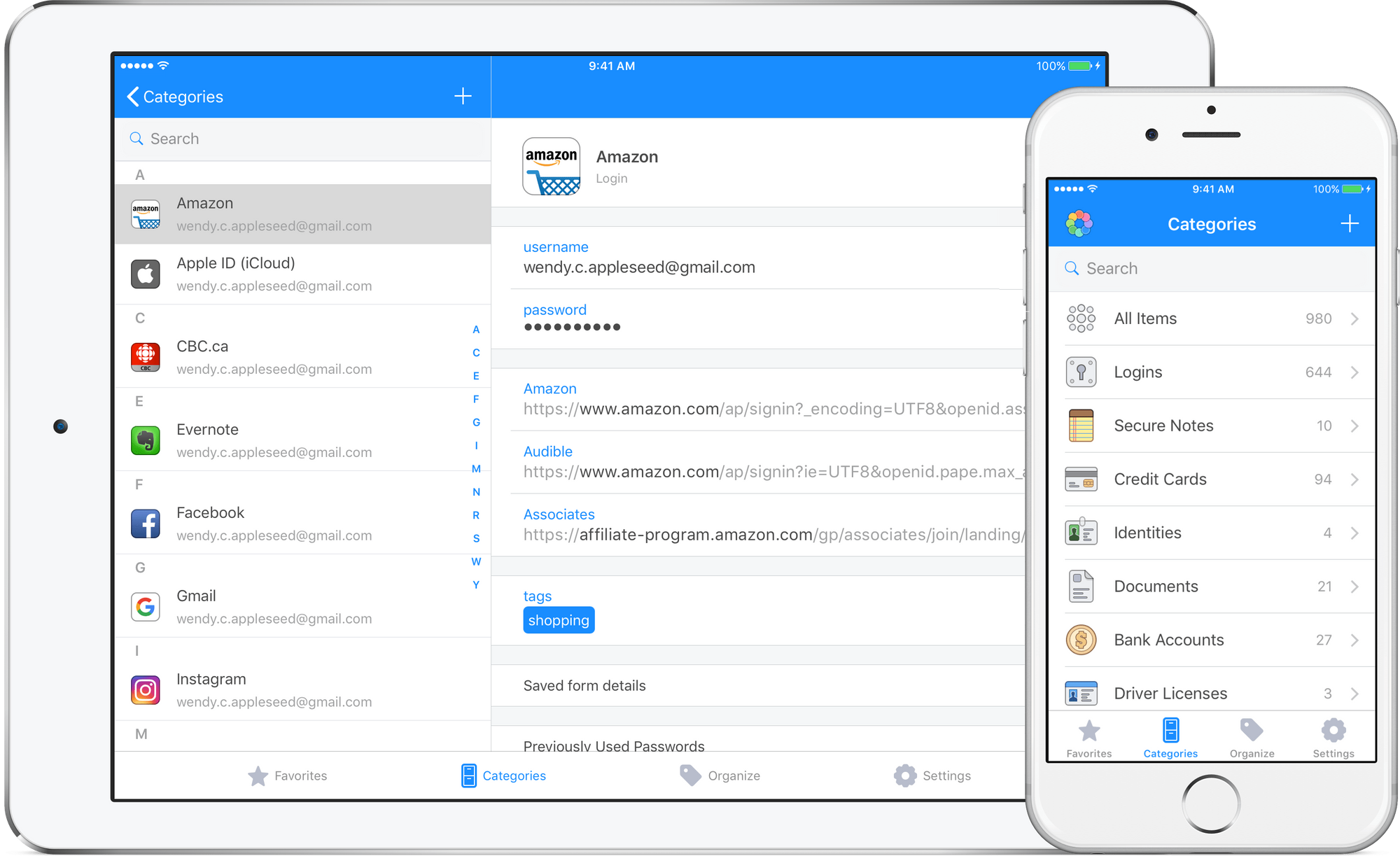
Password managers so your staff will not reuse their passwords everywhere
According to reports, one in every two people are guilty of reusing the password across different websites. The issue is that hackers can buy off username and password combinations (credentials) from the dark web stolen from data breaches. A newly stolen credential can cost as little as $1 per mailbox, criminals will buy these and use them try to log into business email such as Office 365 and G Suite.
If your staff is guilt of reusing passwords, criminals will get in and attempt to defraud you using well established business email compromise and payment redirection techniques. You can avoid this threat by using a password manager.
Our personal favourite is 1Password because it is not only secure, but can warn you if your password end up in a data breach. This feature allows you to change your password as a precaution.
End-user security awareness training
Your staff are your last line of defence If every technical counter-measure fails, or criminals find a way to get around them, or they attack you through your trusted vendors – your staff is your last resort.
We all have weak moments, and even the most cautious people can fall for an email scam. You must educate your employees through information security awareness training to be vigilant, and teach them how they can identify phishing and social engineering attempts.
Phishing simulation to identify vulnerable employees
We suggest combining end-user education with phishing simulation campaigns. Use lifelike phishing campaigns to:
- Identify vulnerable segments of staff; then
- Target at risk staff with training such as e-learning courses, webinars and face-to-face workshops;
- Then measure the effectiveness of the training.
Conclusion
Phishing is not an unsolvable problem. With the right combination of practices, you can prepare and defend your organisation from cyber scams, including phishing and social engineering. Although no system is 100% foolproof, criminals will move onto easier targets because of these measures.
About Iron Bastion
Iron Bastion are Australia’s phishing and cybersecurity experts. We provide cybersecurity consulting with specialised solutions to combat phishing.
Our team are qualified cybersecurity professionals providing phishing awareness training courses and cyber security solutions to small and mid-size businesses.
Contact us for a free cybersecurity consultation today.